Quick Summary
The Tenant Center allows you to deploy your current workspace to multiple tenant environments. Tenants are best utilized for things like separate development, staging, and production environments, or isolating different customers or user groups into their own workspaces, like users in a specific region or your beta testers.Each tenant gets its own isolated database, and receives logic from releases you choose to deploy.Why Tenant Center
What Tenant Center unlocks and when to reach for it
Using Tenant Center
The end-to-end flow: create a tenant, deploy a release, call its APIs
Managing Tenants
Day-2 operations: edit, impersonate, env vars, backups, logs
Tenant Types
Shared, Dedicated, and Remote namespaces, plus infrastructure sizing
Tenant Clusters
Register remote Kubernetes clusters for Regional Isolation tenants
RBAC: Tenant Center
Permissions and common role recipes
Why Tenant Center
The Tenant Center brings a traditional CI/CD workflow into Xano, and gives you a single place to run as many isolated copies of your backend as your business needs — each with its own database, its own URL, and its own lifecycle. With Tenant Center, you can:- Run real dev / stage / production environments for the same workspace, instead of editing live and hoping for the best
- Isolate customers or user groups into their own tenants — perfect for per-customer data isolation, beta cohorts, or rolling out new features to one group at a time
- Deploy across regions to reduce latency for users in another part of the world or to satisfy data-residency requirements
- Stage Xano platform upgrades safely by running a tenant on a newer (or older) platform release and validating against it before rolling that version out everywhere else
Tenant vs. branch vs. workspace
| Use a… | When you need… |
|---|---|
| Branch | An isolated edit state inside the same workspace for a feature or experiment. No separate runtime. |
| Tenant | An isolated runtime with its own database and URL, sharing logic released from a source workspace. |
| Workspace | A fully separate project with its own branches, releases, and tenants. |
Using Tenant Center
This section walks the full Tenant Center flow in the order you’ll actually use it: create a tenant, call its APIs, and deploy a release to it.Creating New Tenants
From your main (usually your production or primary development) workspace, head to the Tenant Center from the left-hand navigation menu.
You’ll find it located under the Marketplace (if you have it enabled) or the Library.
Click Add Tenant to create a new tenant.
Click Add Tenant to create a new tenant.Remember, tenants can be either your own stage and production environments, or actual separate user workspaces.When adding a new tenant, you’ll need to provide some basic information.
| Parameter | Purpose | Example |
|---|---|---|
| Display Name | The name of the tenant workspace | Stage, Beta, Customer ABC |
| Description | A description of the tenant workspace | ”Staging changes for testing” “Workspace for customer ABC” “Beta access” |
| Type | See Tenant Types | |
| Platform | Choose which Xano release you want your Tenant to deploy with. | The latest release is recommended. |
| Cluster | See Tenant Clusters | |
| RBAC Override | Enable this option to set specific user permissions for this tenant. See the RBAC: Tenant Center section below for more information. | |
| Ingress Enabled | Enable or disable ingress (incoming traffic) for this tenant. Disabling ingress will prevent any API calls from reaching this tenant. Use this if traffic is routed through your own gateway/load balancer instead of Xano’s default ingress. | |
| Tags | Apply tags to your tenants to easily filter them when searching and deploying new changes. Great for things like separating subscription tiers or tagging development-specific, internal tenants. This is optional, but highly recommended | dev prod beta |
| Custom Domain | Custom domains require additional setup outside of Xano. Please reach out to support for more details. |
A note on new tenant creation
Creating a new tenant does not deploy a release to it by default.Developing and Deploying Releases
Once you have one or more tenants, you push changes to them by cutting a release from your source workspace and deploying it. A release is a snapshot of logic and schema only — no data — taken from a source branch. Deploying a release to a tenant overwrites its function stacks, APIs, and table structure, but preserves:- Tenant database records
- Environment variables
- Backups
- RBAC overrides
- Ingress and infrastructure settings
Worth a quick read: “release” and “platform” are two different things in Xano.A release (what this section is about) is a snapshot of your workspace logic and schema that you deploy to tenants. A tenant’s platform is the version of Xano itself that tenant is running, chosen via the Platform setting when you create the tenant.The two are completely independent — updating a tenant’s platform won’t deploy your workspace changes, and deploying a release won’t change the platform a tenant is running on.
Preventing Deployment issues
Backups
Backups are available for your tenants by clicking the and selecting Backups. Create a backup by selecting Create New Backup. Backups are designed to be retained long term, and can be downloaded for offline archival. They contain the entirety of the tenant: database and logic.Snapshots
Snapshots are similar to backups, but designed specifically to only retain the database for quick rollback after a deployment, should it be necessary. Snapshots are available for your tenants by clicking the and selecting Snapshots. Create a snapshot by selecting Create New Snapshot. Snapshots are not written back to the tenant — the tenant is ‘swapped’ to that snapshot if you choose to do so, retaining the live database, so you can swap back at any time.** Active connections will be briefly dropped **
To clone the database, the tenant’s live connections are terminated for a few seconds while the copy runs. You’ll need to check the box to agree to this before continuing.
Make any changes you'd like to deploy in your development tenant. Push them to your stage tenant if you're using one.
Just make sure you’re deploying from the tenant that contains your final, tested round of changes to push live to your tenants.
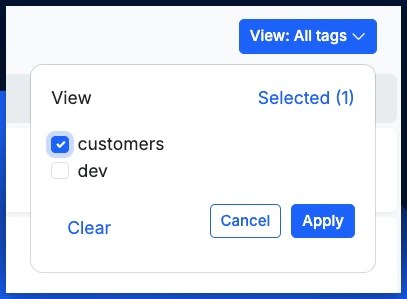
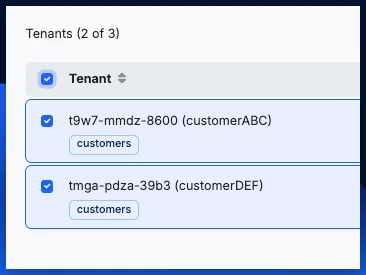
Use the tag selector to filter only the tenants you want to deploy to.
Select the appropriate tags and click Apply. Remember, you can also deploy to a single tenant by clicking the  icon on that specific tenant.
icon on that specific tenant.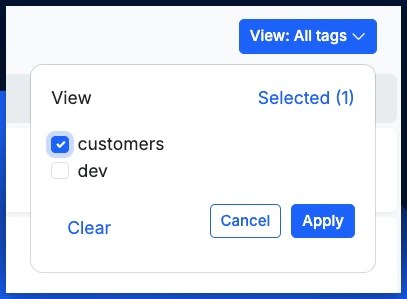
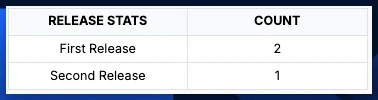
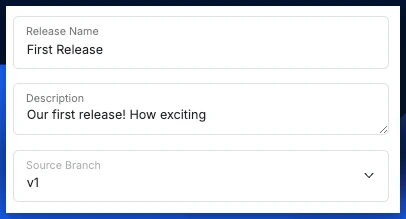
Set up a new release.
Click Releases at the top of the page to open the Releases panel.In the Releases panel, click Add New ReleaseGive your new release a name, a description, and choose the source branch you’ll be deploying changes from.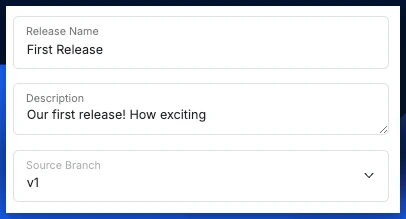 When you’re ready, click Create at the bottom of the panel.
When you’re ready, click Create at the bottom of the panel.
Select the tenants you'd like to deploy to.
You can click the checkbox at the top to select all currently shown tenants, or select individual tenants yourself.When deploying to multiple tenants, deployment runs sequentially. If a tenant fails (for example, an invalid database reference), the deploy stops on that tenant and remaining tenants are skipped — resolve the failure and re-run the deploy against the remaining tenants.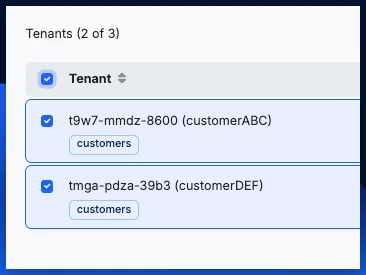
Calling Tenant APIs
Each tenant will have their own base URL, which can be used to call a tenant’s APIs directly. You can find this URL and more by clicking and choosing Details. You can also utilize theX-Tenant header to route a request to a specific tenant instead of using that tenant’s base URL. Set the header as X-Tenant: <tenant name> against your source workspace’s base URL and the request will be routed to that tenant. This is useful when a single frontend needs to target multiple tenants without swapping base URLs.
Managing Tenants
Once you’ve created a tenant, you can click the ⋮ icon to access tenant settings.Edit Tenant
Change the settings applied when creating the tenant, such as the display name or description.| Option | Description |
|---|---|
| Display Name | Change the human readable name of the tenant |
| Description | Edit the tenant description |
| Enable RBAC Override | Allows for tenant-specific RBAC configuration |
| Add or Edit Tags | Use tags for easily searching for related items in your workspace |
| Custom Domain | Add a custom domain (contact support for setup information) |
| Proxy URL | Forward all requests to a different URL |
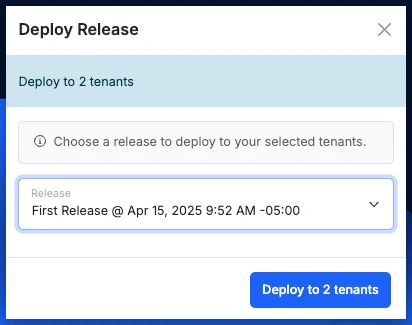
Deploy Release
Push a release (a snapshot of your workspace logic and schema) to this specific tenant. This is the same flow described in Developing and Deploying Releases, scoped to a single tenant. When you open the panel you’ll see:- Release selector — choose any release from the source workspace. Each entry shows the release name, hotfix label (if any), and the timestamp it was created.
- View Changes — opens a diff of the current tenant content versus the selected release so you can review exactly what will change before deploying. If the tenant is already on the selected release, this option is disabled.
- Deploy — runs the deployment. The panel reports per-tenant progress and elapsed time.
- If a release references a database object (table, field, etc.) that doesn’t exist on the target tenant, the deploy fails with a database reference error and the tenant is left on its previous release. Resolve the missing reference and re-run the deploy.
- You can deploy to multiple tenants in one operation from the main Tenant Center view; deployment runs sequentially and stops on the first failure.
- Deploy Release does not change the tenant’s platform version — for that, use Deploy Platform below.
Deploy Platform
Update the Xano platform version this tenant runs on. This is independent of Deploy Release: a release ships your workspace logic, while Deploy Platform updates the underlying Xano runtime the tenant executes against. The panel shows:- Platform selector — choose any available Xano platform version. Each entry shows the platform ID, name, and the date it was published. The selector defaults to the tenant’s current platform.
- Deploy — applies the selected platform to the tenant.
- Stage a tenant on a newer platform version to validate your workspace against it before rolling that version out to production tenants
- Pin a tenant to a specific platform version for stability
- Catch a tenant up to the platform other tenants are already running
Deploy Platform is available on Resource Isolation (Dedicated) and Regional Isolation (Remote) tenants. Shared Namespace tenants run on the same platform as the source instance and don’t expose this option.
Manage Resources
Edit the CPU, memory, storage, autoscaling, affinity, and toleration settings for this tenant’s deployments. Available on Resource Isolation and Regional Isolation tenants. This panel is covered in detail in Configuring Resources for Tenants, including the Small / Medium / Large templates, the Custom editor, per-deployment configuration for the database and Redis instances, the Horizontal Pod Autoscaler fields, and how affinity and toleration rules interact. Two save options are available at the bottom of the panel:- Save — persists your resource changes without redeploying the tenant’s platform.
- Save & Deploy — persists the changes and immediately redeploys the platform so the new resource allocation takes effect. If the tenant has no platform assigned yet, only Save is available.
Infrastructure
A read-only observability view into the live Kubernetes resources backing this tenant. Use it to check pod health, verify a deployment rolled out correctly, look up the tenant’s external IP, or confirm storage is provisioned. The panel is organized into six tabs, each backed by live data from the cluster. A Refresh button at the top reloads the current tab.| Tab | What it shows |
|---|---|
| Pods | Every running pod with current CPU usage, RAM usage, age, restart count, lifecycle phase, and ready status. Click a row to see container images, ports, resource requests/limits, and status history. |
| Deployments | Each deployment with ready vs. desired replica counts and the container image being used. Click through for full container specs. |
| Services | Service discovery details: service type (ClusterIP, LoadBalancer, etc.), cluster IPs, external IP, and exposed ports. Useful for tracing how traffic reaches the tenant. |
| PVCs | Persistent Volume Claims: name, status, capacity, access modes, storage class, and age. This is where you confirm the database’s persistent storage is healthy. |
| Ingress | Ingress configuration: ingress class, hostnames, and the load balancer address or IP that external traffic enters through. |
| Jobs | Kubernetes Jobs associated with the tenant: name, start time, age, completion count, and success count. |
1.2 cores or 850m) and memory in Gi or Mi depending on magnitude.
The Infrastructure panel is read-only — to change any of these values, use Manage Resources or Deploy Platform.
Impersonate
Access the tenant in its current state. Great for troubleshooting tenant-specific issues and manual verification of pushed changesEnvironment Variables
You can access and manage this tenant’s environment variables from here. Use these to store things like API keys and other sensitive information to be used in that tenant’s function stacks. For example, if you are pushing a feature that calls OpenAI, and each tenant has their own OpenAI API key, you’d put that here and just make sure the variable name matches what your function stacks reference.Backups
Create or restore a backup of a tenantLogs
Review logs directly associated with that tenant, such as release deployments, backups, and impersonations.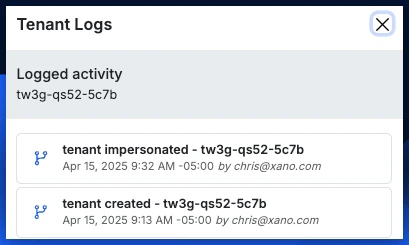
Tenant Types
Some workspaces may have access to different tenant types, which unlock significant operational flexibility beyond the default Shared Namespace. Upgrading to a Dedicated or Remote tenant lets you:- Choose dedicated CPU, memory, and storage so a tenant is insulated from noisy neighbors and can be sized to its actual workload
- Pin a tenant to a specific region for data residency compliance or to reduce latency for users in that region
- Run a tenant on a specific Xano platform release, which is invaluable for safe development — you can stage a tenant on a newer or older platform version and validate your workspace against it before rolling that platform version out to production tenants
What’s available at each tier
| Capability | Data Isolation (Shared) | Resource Isolation (Dedicated) | Regional Isolation (Remote) |
|---|---|---|---|
| Isolated database and base URL | ✓ | ✓ | ✓ |
| Deploy releases from a source workspace | ✓ | ✓ | ✓ |
| Per-tenant environment variables, backups, and impersonate | ✓ | ✓ | ✓ |
| Dedicated CPU, RAM, and storage (no noisy-neighbor effects) | — | ✓ | ✓ |
| Configurable Horizontal Pod Autoscaler | — | ✓ | ✓ |
| Pin to a specific Xano platform version (Deploy Platform) | — | ✓ | ✓ |
| Live infrastructure observability (pods, PVCs, ingress…) | — | ✓ | ✓ |
| Run in a specific region or your own Kubernetes cluster | — | — | ✓ |
| Data residency for compliance use cases | — | — | ✓ |
| Type | Description | Pick this when |
|---|---|---|
| Data Isolation (Shared Namespace) | Shares resources with the source instance. No extra settings. | You need data isolation between customers but the workloads can safely share resources. Lowest overhead. |
| Resource Isolation (Dedicated Namespace) | Gets dedicated resources; you choose allocation after creation. | A tenant has predictable load requirements, SLAs, or noisy-neighbor concerns. |
| Regional Isolation (Remote Namespace) | Runs on dedicated resources in a different cluster/region. | You have data residency requirements or need to reduce latency for users in another region. |
Tenant Infrastructure
When deploying a Resource Isolation (Dedicated Namespace) or Regional Isolation (Remote Namespace) tenant, after creating the tenant you’ll be prompted to select the specific infrastructure allocation for that tenant. We offer three pre-defined infrastructure packages, plus a Custom option:- Small = “Get me live fast.” Best for MVPs, prototypes, internal tools, early-stage production, or moderate traffic.
- Medium = “We’re in production and growing.” For apps with steady real users, more endpoints, more background jobs, and higher concurrency.
- Large = “We need serious headroom.” Built for high traffic, enterprise workloads, heavy automation, larger datasets, and lots of simultaneous users.
- Custom = manually define all aspects of a tenant’s available resources for more advanced configurations.
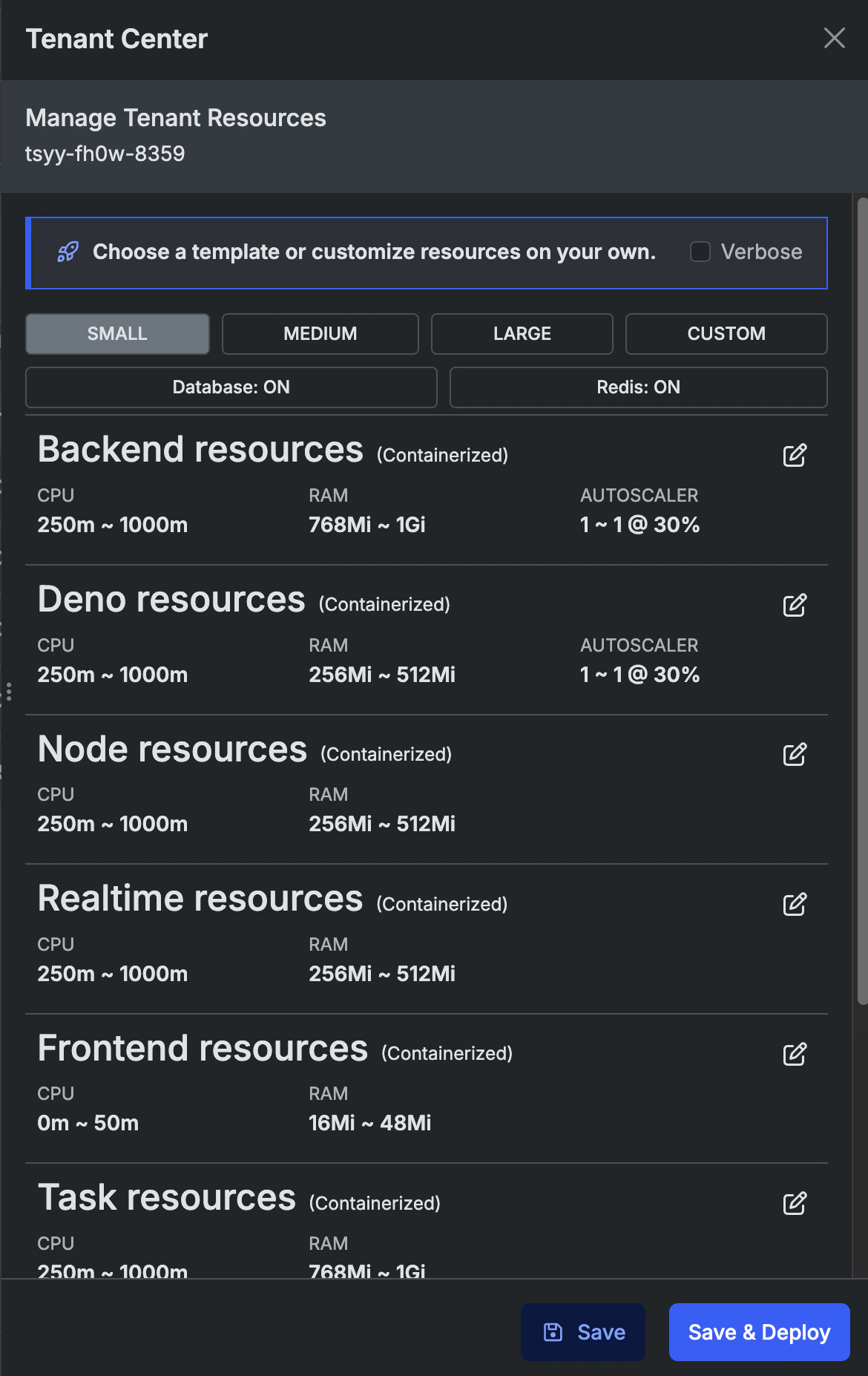
Configuring Resources for Tenants
Resource Isolation and Regional Isolation tenants both run on dedicated infrastructure, which means you control exactly how much CPU, memory, storage, and scaling capacity is allocated to each deployment. After a qualified tenant is created, open its ⋮ menu and choose Manage Resources to open the resource configuration panel.Templates vs Custom
At the top of the panel you’ll see four options: Small, Medium, Large, and Custom.- Clicking Small / Medium / Large applies one of the predefined infrastructure packages described above — a quick starting point for most tenants.
- Any time you change an individual value, the selection automatically switches to Custom, indicating that you’ve diverged from a template. You can return to a template at any point by re-selecting it (this will overwrite your custom values).
- Toggling Verbose at the top reveals additional detail in the summary view, including affinity and toleration rules.
Deployments
A tenant with configurable resources is made up of two independently configurable deployments:- Database — the tenant’s Postgres instance, including persistent storage
- Redis — the tenant’s Redis instance, used for caching and realtime features
CPU and RAM
For each deployment you can configure four values:| Field | Purpose |
|---|---|
| Requested CPU | The minimum CPU Kubernetes guarantees to the container |
| Limit CPU | The maximum CPU the container is allowed to consume |
| Requested RAM | The minimum memory guaranteed to the container |
| Limit RAM | The maximum memory the container is allowed to consume |
Autoscaler (Horizontal Pod Autoscaler)
Deployments that support autoscaling expose an Autoscaler section with three fields:| Field | Purpose |
|---|---|
| Min replicas | Minimum number of pods to keep running at all times |
| Max replicas | Maximum number of pods the autoscaler can scale up to |
| CPU threshold | Target CPU utilization percentage that triggers scale-up |
Storage
For deployments with persistent storage (the database), set the Storage value to the size of the persistent volume. Storage can typically be increased later but not decreased, so start conservatively and grow as needed.Affinity
Affinity rules control which nodes in the cluster your tenant’s pods are allowed to run on. This is especially useful on Regional Isolation clusters where you’ve tagged nodes by zone, hardware class, or customer. Each expression consists of:- Key — the node label to match (e.g.
topology.kubernetes.io/zone) - Operator —
In,NotIn,Exists,DoesNotExist,Gt,Lt - Value — the value (or values) to match against
- Type —
Required(hard constraint; pods won’t schedule without a match) orPreferred(soft constraint; scheduler tries but will fall back)
Toleration
Tolerations let tenant pods run on nodes that have been tainted — for example, nodes reserved for a specific customer or workload class. Each toleration consists of:- Key — the taint key on the node
- Value — the taint value (when applicable)
- Operator —
EqualorExists - Effect —
NoSchedule,PreferNoSchedule, orNoExecute
Saving changes
When you’re finished, click Ok to close the edit view for a deployment, then Save & Deploy (or Deploy if you arrived from another flow) at the bottom of the panel. Resource changes are rolled out immediately, which may cause a brief restart of the affected deployment.Tenant Clusters
A Tenant Cluster is a remote Kubernetes cluster registered with your instance and used to host Regional Isolation tenants (the Remote Namespace type). Tenant Clusters are what make it possible for a tenant created in the Tenant Center to run in a different region, a dedicated production environment, or any other Kubernetes footprint you control. Typical use cases:- Hosting tenants in a specific geographic region for latency or data-residency requirements
- Running isolated production environments separate from your main instance
- Dedicating infrastructure to a particular customer or customer segment
Creating a Tenant Cluster
From the Tenant Clusters panel, click Add new cluster and provide:| Field | Purpose |
|---|---|
| Cluster Name | Display name used when selecting the cluster during tenant creation |
| Description | Optional notes about the cluster’s purpose |
| Type | Standard for on-demand tenants, or Run to keep a pool of pre-provisioned (“warm”) tenants ready for fast assignment |
| Warm Tenants by Template | (Run type only) Number of warm tenants to keep on deck for each template size: Small, Medium, Large, and Custom |
| Domain | Base domain for the cluster. Each tenant deployed to this cluster will be a subdomain of this domain by default (per-tenant custom domains are still supported) |
| Ingress Settings | (Optional) Xano Secret, Xano TLS Host, Custom Secret, Custom TLS Host, and YAML Annotations for the ingress controller. Tenant variables such as {{tenant.name}}.domain.com can be used in any field |
| Credentials (KubeConfig) | The KubeConfig YAML used to authenticate against the target cluster (see below) |
KubeConfig
The Credentials field accepts a standard Kuberneteskubeconfig YAML document — the same file format produced by kubectl config view --raw or by your cloud provider’s CLI (e.g. aws eks update-kubeconfig, gcloud container clusters get-credentials, az aks get-credentials).
Xano uses this KubeConfig to connect to your cluster and provision, update, and remove tenant workloads. A few things to keep in mind:
- Required permissions — the credentials must have sufficient RBAC permissions in the target cluster to create and manage namespaces, deployments, services, ingresses, and secrets.
- Network reachability — the cluster’s API server must be reachable from Xano. If your control plane is behind an IP allow-list, make sure Xano’s outbound IPs are whitelisted before saving the KubeConfig.
- Long-lived credentials — prefer service-account tokens or other long-lived credentials over short-lived user tokens, since Xano needs ongoing access to manage tenants over the cluster’s lifetime.
- Updating credentials — you can rotate the KubeConfig at any time by opening the cluster, clicking Credentials, and pasting the new YAML. This requires the
TenantClusterSecrets: Updatepermission.
Editing and Deleting Clusters
Opening a cluster from the list shows its general settings and ingress configuration. From here you can:- Edit general settings — name, description, type, warm pool sizes, and domain
- Edit Ingress — update ingress secrets, TLS hosts, and annotations independently of the general settings
- Credentials — view or replace the cluster’s KubeConfig
- Delete — remove the cluster registration. Deletion requires typing a confirmation phrase and cannot be undone
How Tenant Clusters relate to the Tenant Center
Tenant Clusters are the infrastructure layer; the Tenant Center is where you create and operate the tenants that run on them. The flow is:- Register a cluster in Tenant Clusters by supplying its KubeConfig, domain, and ingress settings.
- Create a tenant in the Tenant Center and choose Regional Isolation (Remote Namespace) as the type.
- Select the cluster you registered as the target for that tenant.
- Deploy releases to the tenant from the Tenant Center exactly as you would for any other tenant — the release is deployed into the remote cluster transparently.
Permissions
Tenant Cluster management is gated by dedicated RBAC permissions:- TenantCluster — Create, Read, Update, Delete cluster registrations
- TenantClusterSecrets — Read and Update the KubeConfig credentials stored on a cluster
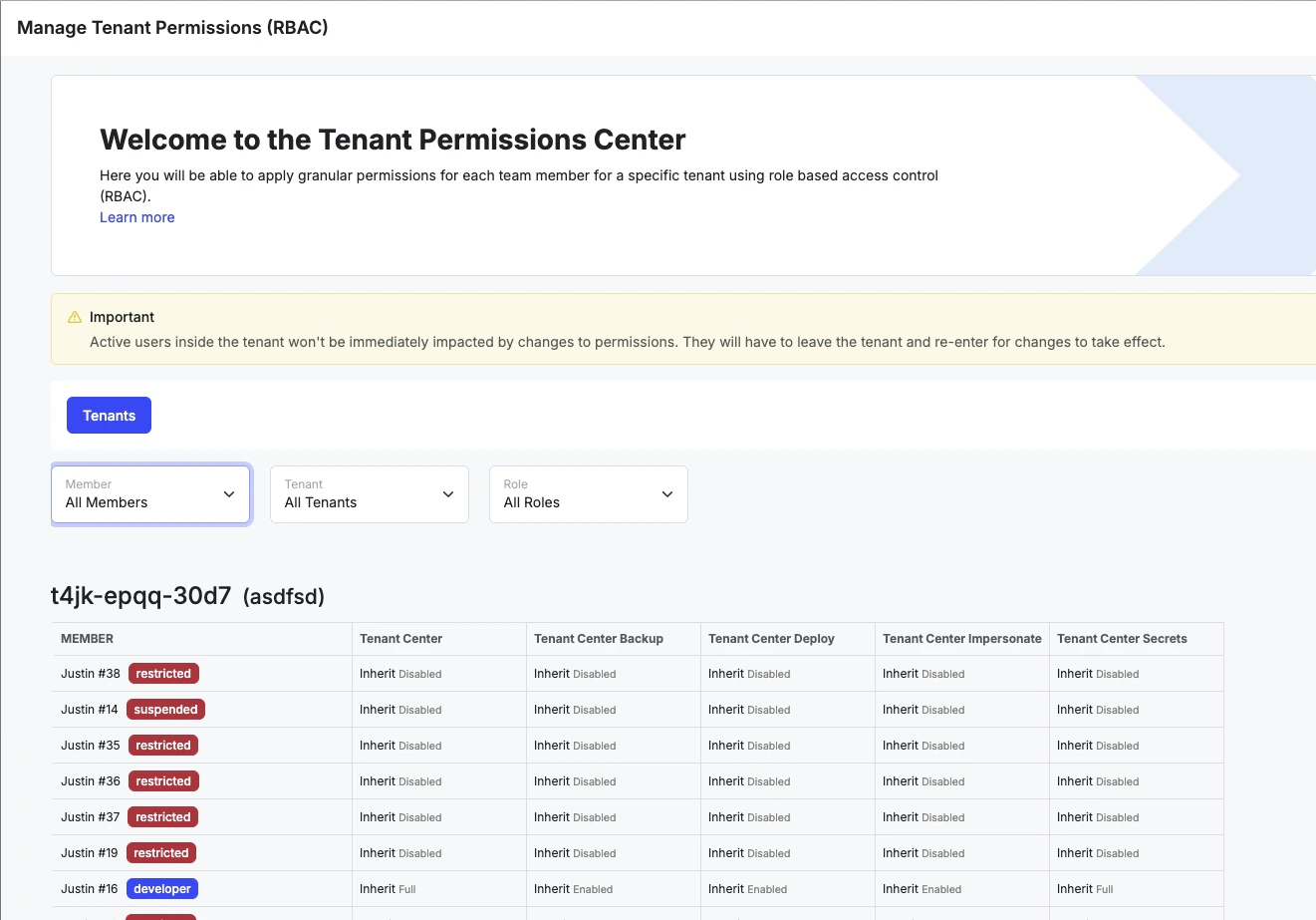
RBAC: Tenant Center
The Tenant Center addon includes additional Role-based Access Control (RBAC) settings you can use to manage tenant-related permissions. These permissions include:- Tenant Center - Enables access to the Tenant Center
- Tenant Center RBAC - Enables access to Tenant Center RBAC Override settings Note: This does not disable the ability to disable/enable Tenant Center RBAC Overrides, but does disable access to editing the specific override settings.
- Tenant Center Logs - Enables access to the logs inside of the Tenant Center
- Tenant Center Backup - Determines if a user can modify backup settings or perform backup/restore operations for tenants
- Tenant Center Deploy - Determines if a user can deploy releases to tenants
- Tenant Center Impersonate - Determines if a user can impersonate (access directly) a tenant
- Tenant Center Secrets - Enables access to secrets for a tenant, such as Environment Variables
RBAC Override
From the Edit Tenant panel, you can enable RBAC Override. This option allows you to specify individual user permissions for each tenant by clicking RBAC at the top of the Tenant Center.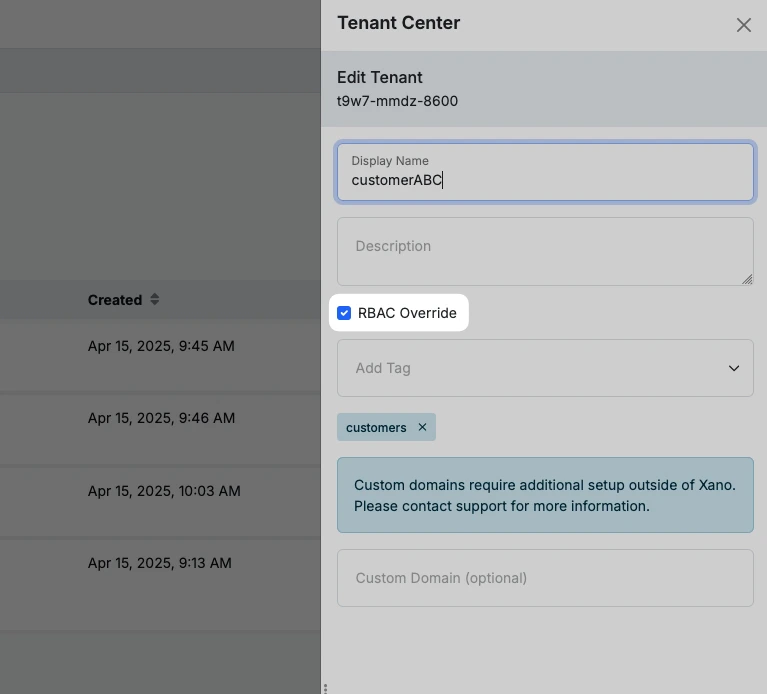
Common role recipes
| Role | Permissions to grant |
|---|---|
| Deploy operator — can ship releases but not change tenant config or read secrets | Tenant Center, Tenant Center Deploy, Tenant Center Logs |
| Read-only auditor — can review tenant state and deploy history without making changes | Tenant Center, Tenant Center Logs |
| Tenant admin — full lifecycle ownership of a tenant including secrets and backups | Tenant Center, Tenant Center Deploy, Tenant Center Backup, Tenant Center Secrets, Tenant Center Impersonate, Tenant Center Logs |
| Support engineer — can impersonate to troubleshoot but cannot deploy or change secrets | Tenant Center, Tenant Center Impersonate, Tenant Center Logs |
Best Practices
Tag your tenants
Using tags is crucial to quick and consistent work inside of the Tenant Center, especially as the number of tenants you have grows.
Follow a traditional deployment framework
This would include developing on a development tenant, pushing final changes to a stage tenant where all of your QA and testing happens, and then deploying releases from stage.Read more about the entire Development Lifecycle here.